The era of “seeing is believing” ended quietly, then all at once. In early 2026, the internet reached a saturation point where the cost of generating a photorealistic, high-fidelity deepfake dropped to nearly zero, while the speed of dissemination hit an all-time high. We are no longer just fighting “fake news”; we are fighting a total collapse of digital reality. When a video of a CEO making a market-moving announcement or a politician giving a speech can be fabricated in seconds on a consumer-grade laptop, the very infrastructure of public trust begins to crumble.
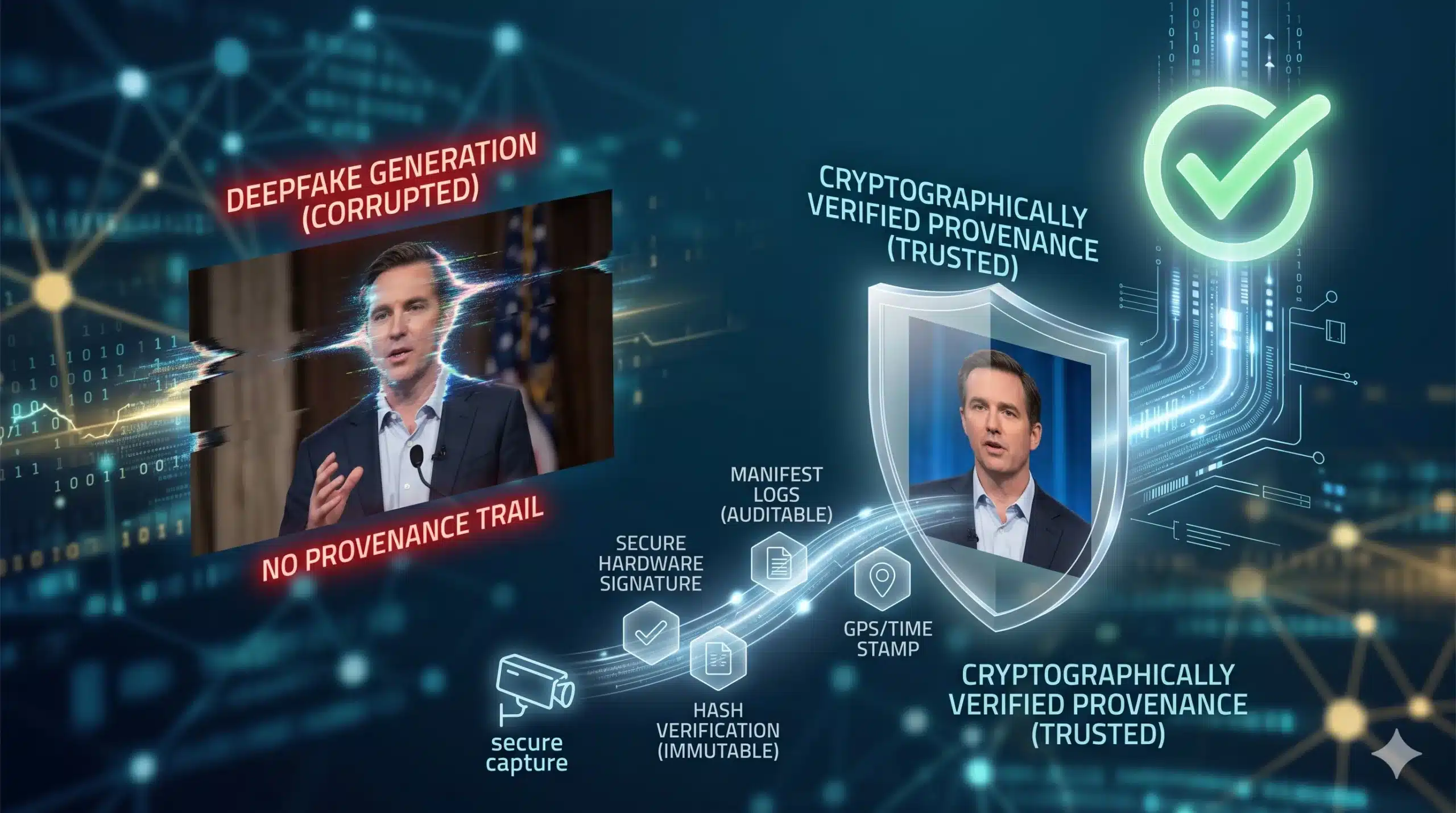
We are now entering the age of Digital Content Provenance. The strategy has shifted from trying to “detect” fakes—an exhausting game of cat-and-mouse—to “verifying” the truth. By attaching an immutable, cryptographically secure digital birth certificate to every piece of media, we are rebuilding the internet’s ecosystem around a new mandate: if it isn’t signed, it isn’t real.
The “Why”: The Failure of Detection-Based Defense
The economic and social drive for provenance standards is rooted in the “Detection Paradox.” For every new AI detector developed, a more sophisticated generative adversarial network (GAN) is born to bypass it. Relying on detection is reactive; it requires the damage to be done before a “fake” label can be applied. For businesses, the ROI of a proactive defense is clear: preventing a fraudulent wire transfer or a brand-destroying deepfake is significantly cheaper than damage control.
Technologically, the shift is driven by the global adoption of the C2PA (Coalition for Content Provenance and Authenticity) standard. Major tech players, from camera manufacturers to social media giants, have realized that without a unified integration of trust, the commercial value of digital media will evaporate. We are moving from a “post-truth” era to a “verified-origin” era, where the metadata of a file is just as important as the pixels themselves.
Technical Breakdown: How Content Provenance Works
Digital provenance doesn’t hide the truth; it seals it. Unlike traditional metadata, which can be easily stripped or edited, new provenance standards use a “glass-to-glass” cryptographic chain.
- Secure Capture: The process begins at the hardware level. When a photo is taken, the camera’s secure enclave signs the file with a private key, capturing the exact time, GPS location, and sensor data.
- Manifest Logs: Every time the file is edited (cropped, color-corrected, or compressed), an entry is added to a “manifest.” This creates a transparent history of every change made to the media.
- Cryptographic Hashing: The file is linked to a unique hash. If even a single pixel is altered without being logged in the manifest, the “seal” is broken, and the file is flagged as unverified.
- Cloud-Side Verification: Major platforms utilize a distributed infrastructure to cross-reference these hashes against a public ledger, allowing users to click a “Verify” button and see the full “ingredients list” of the media.
The Trust Paradigm Shift
| Feature | Legacy Media (2010–2024) | Provenance-Enabled Media (2026+) |
| Trust Model | Implicit (Assume Real) | Explicit (Assume Fake until Verified) |
| Security Layer | Strippable Metadata (EXIF) | Cryptographic Manifest (C2PA) |
| Edit History | Hidden / Opaque | Transparent / Auditable |
| Verification | AI Detection (Probabilistic) | Cryptographic Signing (Deterministic) |